Secure your Apps and Information
With the emerging evolution in technology, security is becoming a major concern to deal with. Identity security providers can’t achieve the desired level of security requirements for their clients’ IT ecosystem as a firewall and antivirus are not enough. IT admins thus moved to Multi-factor Authentication (MFA) to meet the numerous identity security challenges. Usually, MFA is referred to as 2FA and has been considered as a different entity for IT admins to buy and then implement. Cloud IAM facilities lifted the barrier and tightly integrated multi-factor authentication for securing cloud identities for enterprises.
Robust Access Request Provisioning:
With the upsurge in frequent cybercrime incidences with enterprises – information and identities are always vulnerable to breaches. With the right provisioning of access requests, the threats can be brought down considerably.

What is Provisioning Access Request?
Access Request Provisioning is the process of allowing the rightful users, devices, applications, roles to access enterprise accounts through various permissible modes of logins (user IDs, social accounts, biometrics/voice or face recognition, etc.). When a new employee joins an ID is created and role(s) is assigned with adequate permissions attached to that specific role. When a user attempts a request beyond the permitted role, the request is verified before being approved or rejected by the IT admin.
Throughout the employee lifecycle of any said user roles and accesses keep on changing depending on entry, transfer, promotion, movement within the company, and finally exit. To prevent misuse of access post-exit access request provisioning is at place and ensures that there are no security breaches. Provisioning is revoked from all the users after they leave the organization.

Key Components of Provisioning Access Request
-
It helps minimize audit and compliance costs, rectify and mitigate conflicts for roles/users, offer detailed reports of access risks and controls for better communication with decision-makers, prevent chances of errors and frauds, as well as analyze, manage, and lower risks through rule sets.

-
User access review, SoD review, effective request approval through automated workflow for user provisioning, and unburdening the IT team through automated user access request processing are done in this method.

-
SoD conflicts resolution, using firefighters during additional authorization requirements, automated audit documentation – saving resources, time, and money, and monitoring of firefighters’ activities as well as reviewing and signing off the firefighter logbook for audit are taken care of in this process.

-
Enterprise can enable preventive measures through simulation functionalities, create a varied range of roles by effectively bypassing SoD risks, definition and documentation support for role information, authorization as well as testing outcomes, and uses pre-defined design role methodology and workflow for role design.

Why Avancer Access Request Provisioning?
IAM Access request provisioning ensures identity security and better management of enterprise resources and related information that propels business growth and productivity in multiple verticals. The most notable benefits of Avancer Provisioning Access Request are –
- Saving unnecessary IT resource expenditures
- Enhanced IT operations efficiency
- Improved productivity of employees
- Seamless security and compliance
- Better security within the enterprise
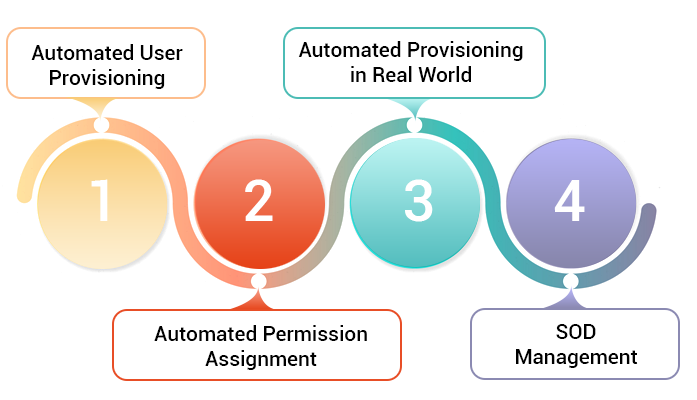
Provisioning Access Request Methods
Provisioning Access Requests robustly protecting your enterprise!
For more information on Avancer Provisioning Access Request.
